Social Media Threat Intelligence: How Organizations Detect Risks Before They Escalate
TL;DR - Quick Answer
14 min readStep-by-step guide. Follow it to get results.
Social Media Threat Intelligence: Detect Risks Before They Escalate
A fake executive account on LinkedIn sends phishing links to your clients. A disgruntled employee leaks proprietary data on Reddit. A coordinated attack campaign targets your brand on Twitter.
By the time your team finds out, the damage is done. Social media threat intelligence catches these threats early, often before they cause harm.
Create content, post everywhere
Create captions, images, and videos with AI. Schedule to 9 platforms in seconds.
Start your free trial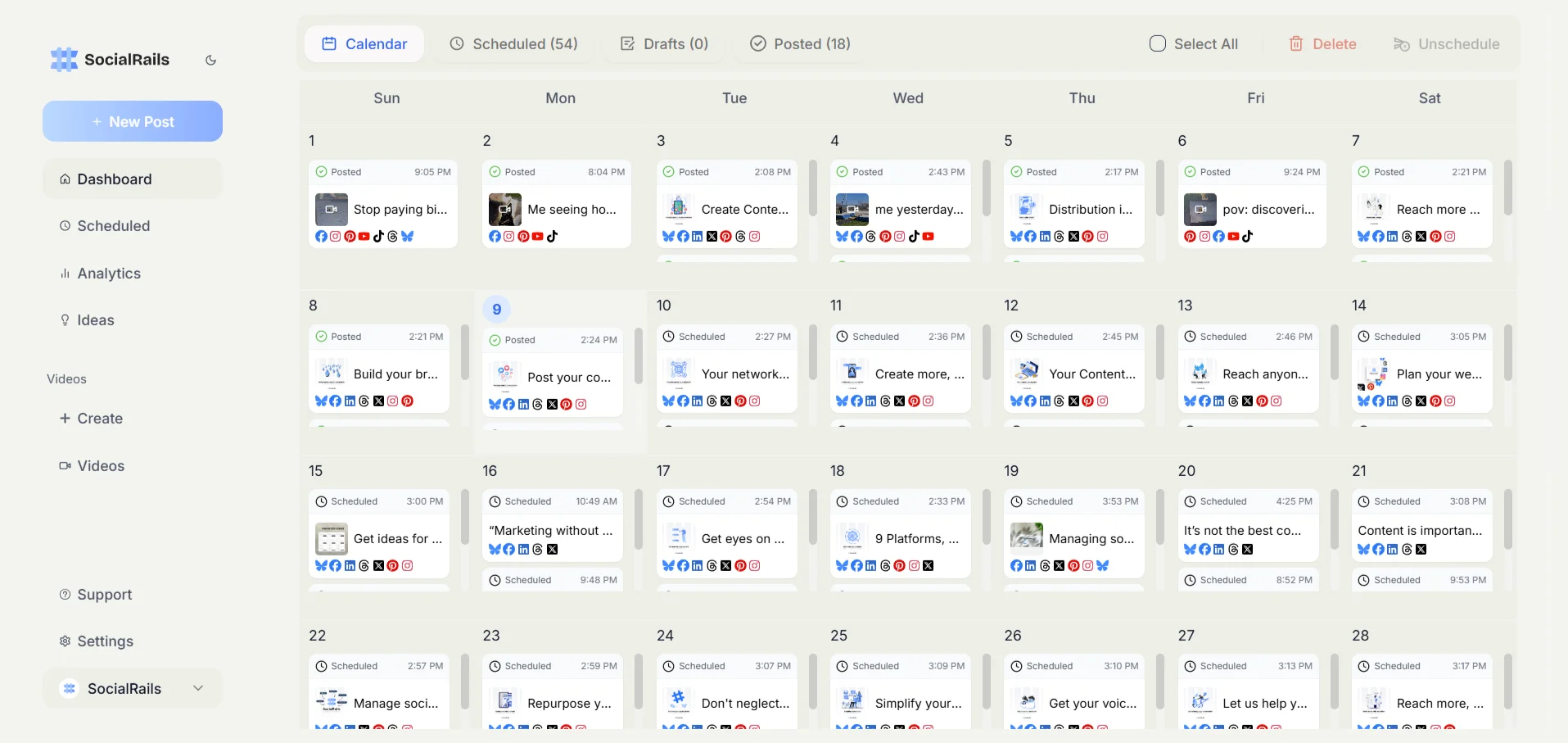
What Is Social Media Threat Intelligence?
Social media threat intelligence (SMTI) is the process of collecting, analyzing, and acting on threat data from social media platforms to protect your organization's people, brand, data, and operations.
It goes beyond brand monitoring. While brand monitoring tracks mentions and sentiment, threat intelligence focuses on:
- Security threats, phishing, malware distribution, credential theft
- Brand impersonation, fake accounts, spoofed domains
- Data exposure, leaked credentials, proprietary information
- Physical threats, threats against executives, facilities, events
- Disinformation, coordinated campaigns to damage reputation
- Insider threats, employees sharing sensitive information
What's the key difference between brand monitoring and social media threat intelligence?
💡 Tip: Think carefully before selecting your answer!
Why It Matters
Social engineering is one of the most common attack vectors, and social media gives threat actors direct access to employees and customers.
The cost of not monitoring:
Threat actors openly sell stolen data, credentials, and exploits on social platforms. Social media is a major channel for phishing outside of email. Executives and public-facing employees are frequent targets for impersonation.
6 Core Capabilities
1. Brand Impersonation Detection
What to monitor:
- Fake accounts using your brand name, logo, or executive identities
- Typosquatted domains promoted via social posts
- Counterfeit product listings shared on social platforms
- Fake customer support accounts targeting your customers
Detection methods:
- Automated scanning for accounts mimicking brand assets
- Logo detection using image recognition
- Domain monitoring for look-alike URLs shared socially
- Keyword alerts for brand name + suspicious terms
2. Phishing and Scam Monitoring
Watch for links to credential harvesting pages shared via social, fake job postings using your company name, social engineering campaigns targeting employees, and malicious ads impersonating your brand.
When you find it:
- Report and take down fake accounts immediately
- Alert affected customers or employees
- Document evidence for law enforcement
- Update security awareness training
3. Data Leak Detection
Sources to monitor:
Where are leaked corporate credentials most commonly shared first?
💡 Tip: Think carefully before selecting your answer!
4. Executive Protection
Executives face doxing (personal information exposure), direct threats, deepfakes using their likeness, stalking, and reputation attacks.
Protective measures:
- Monitor mentions of executives across all platforms
- Track personal information exposure
- Alert on threatening language patterns
- Coordinate with physical security teams
5. Misinformation and Disinformation Tracking
Signs of a coordinated campaign:
- Sudden spike in negative mentions from new or bot accounts
- Identical messaging across multiple accounts
- Artificial amplification patterns
- Cross-platform coordination
- Use of manipulated media
6. Competitive and Geopolitical Intelligence
Legitimate monitoring includes tracking industry threat trends, learning from competitor security incidents, watching geopolitical events that affect operations, and identifying supply chain risks.
Social Media Threat Intelligence Tools
For basic sentiment and brand monitoring, try our Social Media Sentiment Analysis and Sentiment Analysis Tool. For a deeper comparison of monitoring platforms, see our Social Listening Tools Guide and Media Monitoring Tools.
Step-by-Step: Build Your Program
Step 1: Define Your Threat Model
What are you protecting? Brand and reputation, executive safety, customer data, intellectual property, physical locations, employee security. Rank these by risk and impact.
Step 2: Set Your Monitoring Scope
Platforms to cover:
- Major social networks (LinkedIn, X, Facebook, Instagram, TikTok)
- Messaging apps (Telegram, Discord, Signal)
- Forums (Reddit, industry-specific)
- Paste sites and code repositories
- Dark web marketplaces (requires specialized tools)
Keywords to track:
- Brand name + variations and misspellings
- Executive names
- Product and domain names
- Employee email patterns
- Industry-specific threat terms
Step 3: Set Alert Thresholds
Not every mention is a threat. Define escalation criteria:
Step 4: Build Response Playbooks
For each threat type, document who gets notified, the escalation path, evidence collection steps, takedown procedures, communication templates, and post-incident review.
Step 5: Integrate With Existing Security
Connect SMTI with your Security Operations Center, incident response team, legal department, communications/PR, physical security, and HR (for insider threats).
What should be the FIRST step when building a social media threat intelligence program?
💡 Tip: Think carefully before selecting your answer!
Use Cases by Industry
Financial Services: Fake banking apps, account takeover campaigns, cryptocurrency scams using brand names, insider trading discussions.
Healthcare: Patient data leak detection, fake pharmacy accounts, misinformation about treatments, facility threat monitoring.
Government: Disinformation campaign detection, threat assessment for public officials, civil unrest monitoring, foreign influence operations.
Retail & E-Commerce: Counterfeit product listings, fake promotion scams, customer data exposure.
Technology: Source code leak detection, zero-day exploit discussions, employee credential monitoring, vulnerability disclosures.
Measuring Effectiveness
Getting Started
- Audit your current exposure, search your brand, executives, and products across major platforms with our Social Media Audit Template
- Set up basic monitoring, use Social Media Analytics and brand alerts
- Identify your biggest risks, brand impersonation? Data leaks? Executive threats?
- Choose tools that match your threat model, start with one focused tool, expand coverage
- Train your team, security awareness includes social media threats
- Review and refine, do monthly threat reviews and adjust your monitoring scope
Related reading:
Was this article helpful?
Let us know what you think!
